Last week, the Electronic Frontier Foundation filed complaints against Google with the Attorneys General of California and New York. The reason: Google handed a Ph.D. student’s private data to Immigration and Customs Enforcement without telling him — breaking a nearly decade-long public promise to notify users before sharing their information with law enforcement. The student, Amandla Thomas-Johnson, had attended a pro-Palestinian protest at Cornell University for all of five minutes. He was accused of no crime. He has since fled the country. ICE still has his data.
This is not an edge case. This is the system working exactly as designed. And it is an invitation — perhaps the most urgent one of this decade — to build something different.
The Promise Was Always Conditional
We were told the platforms were neutral tools. We were told the data we generated — our searches, our emails, our locations, our associations — would be protected by corporate policy, by terms of service, by promises made in press releases. But a promise is not a structure. A policy is not infrastructure. And when power comes knocking with a subpoena, even informal requests, policies fold like paper.
ICE did not need a court order to get Thomas-Johnson’s data. They sent an administrative subpoena — a request without judicial oversight — and asked Google not to notify the target. Google complied. The law did not require this. The company chose it. That distinction matters enormously: what collapsed here was not a legal safeguard but a voluntary one. A vow made in good times, abandoned in hard ones.
Meanwhile, Congress is in open chaos over Section 702 of the Foreign Intelligence Surveillance Act — the law that allows national security agencies to collect communications between Americans and foreigners without a warrant. A rare coalition of progressive Democrats and hardline Republicans has been fighting to add warrant requirements for Americans’ communications swept up in the dragnet. As of this week, they could not agree on a long-term path and passed a 10-day stopgap. The program nearly expired. The battle is not over.
What both stories reveal is the same truth: the surveillance state does not need to be omnipotent. It only needs the platforms we already use to cooperate. And cooperation, when sufficiently pressured, is the default behavior of centralized infrastructure.
Sovereignty Begins at the Stack
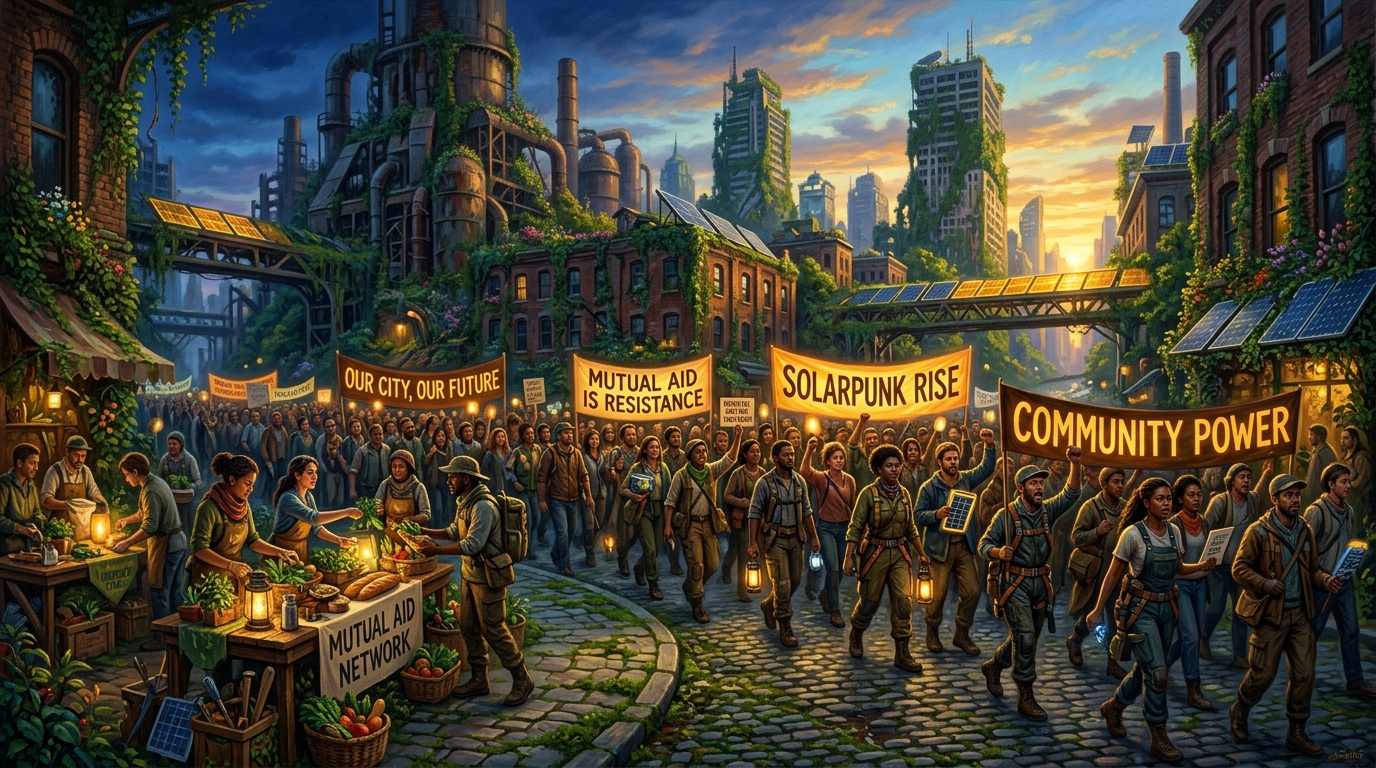
The solarpunk imagination has always understood something that mainstream politics keeps forgetting: who controls the infrastructure controls the community. Water, food, energy — and now data. The struggle for digital autonomy is not separate from the struggle for land, for labor, for housing. It is the same struggle translated into a different medium.
The open-source ecosystem for activists has never been richer. Signal remains the gold standard for encrypted communication — end-to-end, by default, for everyone. Tor Browser routes your traffic through a decentralized relay network that makes surveillance exponentially more difficult. Cryptpad and Nextcloud offer encrypted, self-hostable alternatives to Google Docs and Drive — tools you can run on hardware you control, in a basement, a community center, a rented server in a country with stronger privacy law. OnionShare lets you move files peer-to-peer over Tor, no corporate intermediary required. Tools like VeraCrypt can protect an entire device from forensic extraction.
None of these tools are perfect. None of them make you invisible. But they fundamentally change the cost-benefit equation for any entity trying to surveil a movement. They make mass surveillance expensive. They force the state to expend real resources on individual targets instead of bulk-collecting the entire haystack. That friction is not nothing. That friction has protected organizers, journalists, and dissidents across contexts far more hostile than anything most Americans have yet faced.
The Community Is the Infrastructure
Technology alone does not build resilience. Mutual aid networks organizing across Sudan’s takaaya community kitchens, Black-led rapid response cells activating during Minnesota’s Operation Metro Surge, digital security circles training immigrant rights organizers in the Pacific Northwest — these are the structures that make technology meaningful. Encrypted tools in the hands of isolated individuals are useful. The same tools embedded in a trained, trusting community are transformative.
This is the lesson the surveillance state does not want widely understood: decentralization is not just a network topology. It is a social practice. A movement that has distributed trust — where no single node holds all the names, all the plans, all the relationships — is a movement that cannot be decapitated. Google can hand over one person’s data. They cannot hand over a thousand relationships woven through offline trust and community memory.
The answer to the Google-ICE betrayal is not to sue Google, though the EFF’s complaints to state Attorneys General are a necessary holding action. The answer is to make Google irrelevant to the infrastructure of dissent. To route around the platforms that will fold. To build the community kitchens of digital life — federated, encrypted, distributed, and held in common.
Build the World That Cannot Be Subpoenaed
The Section 702 fight will continue. The FISA debate will return, messier and higher-stakes. ICE will send more administrative subpoenas. And somewhere, a student, an organizer, a mutual aid coordinator will be targeted through data they believed was protected by a promise.
What we can do, today, is shrink the attack surface. Migrate communications to tools that cannot be compelled to betray you because they are architecturally incapable of it — end-to-end encryption means even the service provider cannot read your messages. Host your own infrastructure when you can. Train your community in digital hygiene not as a paranoid exercise but as an act of collective care. Because that is what it is: care for one another, expressed in the language of cryptography and decentralized architecture.
The platform was never yours. But the network can be. Build it like you mean to keep it.